Zero trust model combats changing business & technology landscape
Today’s enterprises conduct business and use digital technologies in ways that are evolving constantly. This digital transformation is making traditional perimeter-based cyber security IT infrastructure redundant. The days when every user and every device sitting inside the organisation’s premises or firewall can be automatically trusted, are over for good.
Today enterprises operate in a very different way. They are more global than ever before and employees are much more distributed – with remote and hybrid working the norm. This trend was already underway before the pandemic hit but has accelerated in the last two years as a result of Covid.
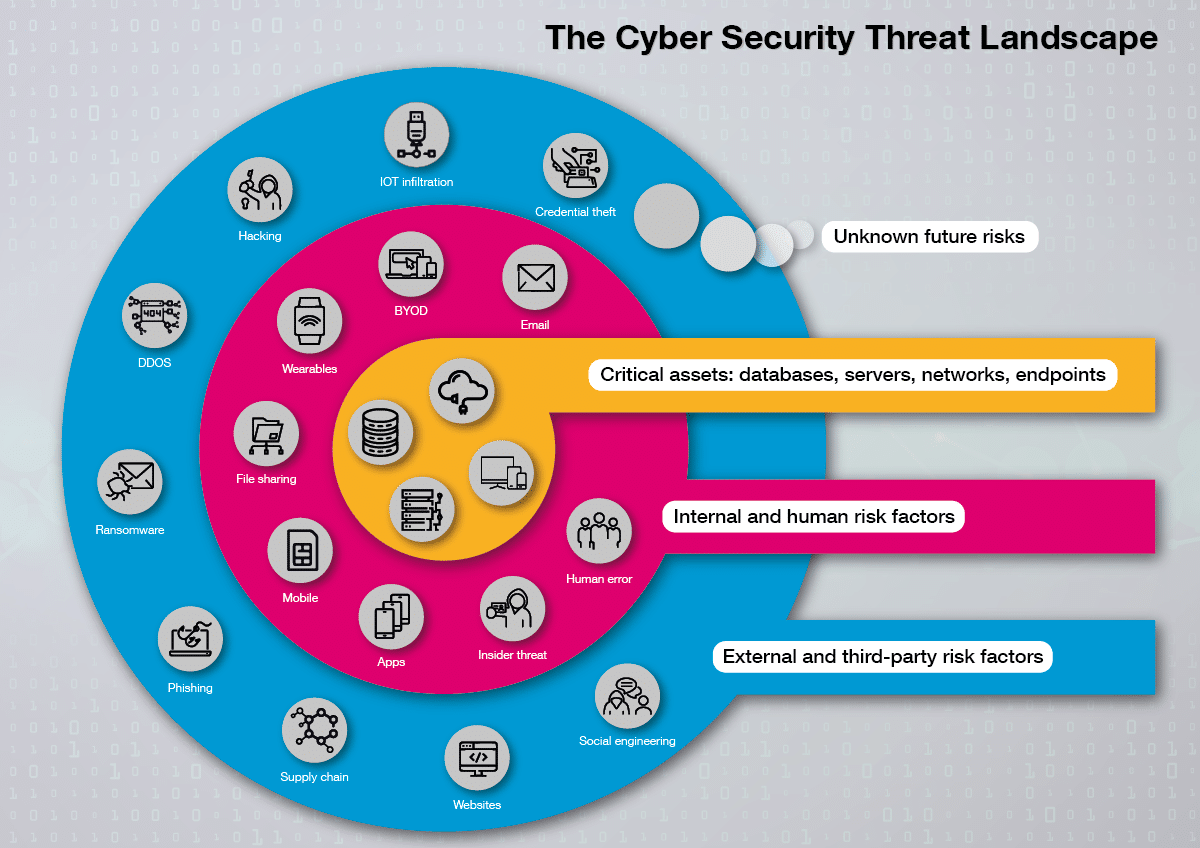
The move to cloud and more distributed environments means that the use of potentially unsecured Wi-Fi networks and devices increases security risks exponentially. The attack surface for cyber threats has grown significantly as businesses have added cloud applications and storage, and as users have switched to accessing corporate tools and information on portable devices. Add in automated, AI-guided malware creation by sophisticated cyber criminals and even nation states, and it’s easy to see that today’s cyber security teams face an unprecedented challenge.
Ransomware attacks will happen every 2 seconds in 2031
In parallel, the escalating threat landscape is creating record threat levels as hackers take advantage of the rich pickings a distributed environment creates. As a result, cybercrime has intensified, and a record-breaking number of ransomware attacks of increasing severity are taking place year-on-year. In fact, according to Cybersecurity Ventures, ransomware is expected to attack a business, consumer, or device every 2 seconds by 2031, up from 11 seconds in 2021. Global ransomware costs are expected to rise from $20 billion in 2021 to $265 billion by 2031.
Global ransomware costs are expected to rise from $20 billion in 2021 to $265 billion by 2031. Share on XManaging all these risks while providing responsive information services to employees, partners and customers is becoming ever more challenging. Likewise, traditional approaches to cyber security which tend to focus on securing the network perimeter against known threats are no longer effective against ubiquitous, fast-changing cyber risks. In this new environment more and more enterprises are now adopting a new approach to cyber security and implementing a Zero Trust model which wraps security around every element of the network.
Taking an ‘always verify’ approach to security
Zero Trust is a security concept centred on the belief that an organisation should not automatically trust anything inside or outside its perimeter and instead must verify anything and everything trying to connect to its systems before granting access. Without an overarching model like a Zero Trust framework, employees working in a secure environment can no longer be verified — or controlled. Zero Trust employs least-privilege and “always-verify” principles, offering complete visibility within the network, whether in data centres or the cloud.
This approach is undoubtedly a challenge for most large enterprises with established IT teams that have worked on a ‘trust but verify’ basis using corporate firewalls and VPNs. Making this change in direction and moving towards a Zero Trust architecture is a big step, but in our view adopting this approach brings many benefits. Additionally, with the proliferation of security tools, frameworks and practices—often within functional silos—it’s next to impossible for security teams to manage the complexity, speed and volume of threats and alerts.
Balancing risk and productivity with a zero trust model
Zero trust is a foundational concept that accepts the need to balance risk and productivity. Treating every device, system, network element and user as a potential threat, zero trust assigns the appropriate level of privileges to facilitate work without exposing the whole organisation to unmanageable risk.
Zero trust wraps layered, proactive, AI-powered security around every user and every element in your infrastructure. It brings all information and controls across the organisation’s hybrid infrastructure into one place, providing a clear real-time view of risk and the ability to respond rapidly and decisively to emerging threats.
Taking a layered approach to security
Here at Northdoor we have a comprehensive portfolio of targeted zero trust solutions that enable customers to apply layered security to every user, device, application, database and access point, which means they can detect and halt attacks wherever and whenever they occur. This also enables organisations to proactively hunt and destroy potential threats before they strike, as well as gain a clear view of present and future risk; using AI to triage these threats. This means organisations can balance risk, productivity, security and privacy throughout their environment.
Without a doubt in 2022 security will be high on the C-Suite agenda. With intensifying trade disputes, an escalating threat landscape, a highly distributed workforce, supply chains stretched to breaking point and other escalating geo-political issues including the Russia:Ukraine conflict, having a secure, productive, agile and cost-effective security framework in place will be paramount.
Want to receive a free, no-obligation assessment of your organisation’s current security positioning? Centred around a zero trust approach, Northdoor can help assess and improve your cyber security systems and processes.