Projected cryptographic break year
Of enterprises unprepared for quantum risk
Global economic data at potential risk
Average time to migrate encryption
Quantum computing is reshaping what's possible and what's vulnerable. Northdoor helps organisations understand the risks and take decisive steps towards cryptographic resilience.
Understanding the technology
A normal computer works by processing information as ones and zeros — every calculation is a sequence of yes/no decisions made at speed. It’s fast, but it’s still working through problems one step at a time.
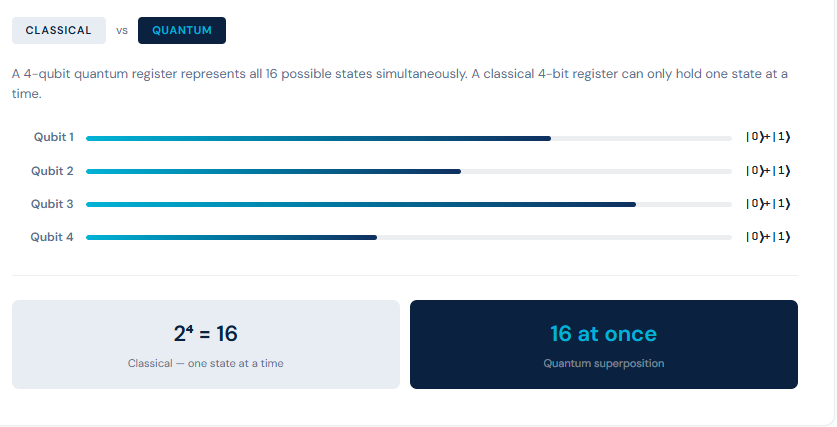
A quantum computer works differently. Instead of ones and zeros, it uses quantum bits — qubits — which can represent many possible states at the same time. That means instead of testing answers one by one, a quantum computer can explore vast numbers of possibilities simultaneously.
For most everyday tasks, that difference doesn’t matter. But for certain types of problem, cracking complex mathematical puzzles, for instance, quantum computers are not just faster. They are a different category of machine entirely.
That matters to your organisation because the encryption protecting your data today is built on exactly those kinds of mathematical puzzles. Problems that would take a classical computer longer than the age of the universe to solve. A sufficiently powerful quantum computer could solve them in hours.
That capability doesn’t exist at full scale yet. But it’s coming. And the data being stored now will still need to be protected when it does.
Classical computers use binary bits — either 0 or 1. Quantum computers use qubits, which can exist in a superposition of both states simultaneously, enabling massively parallel computation at scales impossible for today’s hardware.
Qubits can be entangled, meaning the state of one instantly influences another regardless of distance. Combined with quantum interference, this allows algorithms to rapidly converge on correct answers by amplifying right paths and cancelling wrong ones.
Where classical computers scale linearly, quantum machines scale exponentially. Problems in cryptography, drug discovery, financial modelling, and logistics that are intractable today become solvable in entirely new ways.
IBM, Google, and others now offer quantum systems with hundreds of qubits. Nation-states are investing billions. This is not a distant future — it is an imminent strategic reality for every organisation that holds sensitive data.
Enterprise risk
Quantum computers capable of breaking today’s encryption standards are approaching fast. The risks are not theoretical — adversaries are already harvesting encrypted data today, waiting for quantum capability to decrypt it tomorrow. The time to act is now.
Encryption rendered obsolete
RSA and ECC encryption — the bedrock of internet security, banking, and enterprise communications — can be broken by sufficiently powerful quantum machines using Shor’s algorithm. Data protected today may be fully exposed tomorrow.
● Critical risk
Payment systems, trading infrastructure, SWIFT messaging, and digital contracts all rely on cryptographic protocols that are now vulnerable to quantum attacks. Financial institutions face systemic risk without proactive migration strategies.
● Critical risk
Nation-state actors and sophisticated threat groups are already intercepting and storing encrypted communications today. When quantum capability arrives, years of harvested data — IP, contracts, personal data — become instantly readable.
● Active threat now
Regulators, including NIST, NCSC, and the EU, are mandating transitions to post-quantum cryptography. Organisations failing to act face compliance failures under DORA, NIS2, and emerging quantum-specific regulatory frameworks.
● Emerging mandate
Patient records, genomic data, and personal health information held in long-term, encrypted storage are particularly vulnerable. The sensitivity and longevity of health data makes it a prime target for harvest-now, decrypt-later strategies.
● High risk
Energy grids, transport systems, water treatment, and government communications all depend on encryption quantum computers could break. Migration timelines for these systems are measured in years, and the window to act is narrowing fast.
● National security risk
The path to resilience
IBM Quantum Safe provides the technology, tooling, and strategy to begin your cryptographic transformation today. Northdoor, as an established IBM partner, deploys and operationalises these capabilities across your entire estate from discovery through to long-term cryptographic agility.
1. Discover your cryptographic inventory:
IBM Quantum Safe Explorer scans your applications, libraries, and infrastructure to build a complete Cryptography Bill of Materials (CBOM) — giving you full visibility of every algorithm, key, and certificate in use across your environment before you can remediate.
2. Analyse and prioritise vulnerabilities:
IBM Guardium Quantum Safe maps your cryptographic assets against emerging quantum threats, identifies policy violations, and prioritises remediation based on business impact, helping you focus limited resources precisely where they matter most.
3. Remediate without rewriting code:
IBM Quantum Safe Remediator deploys an adaptive proxy that secures communications and protects applications without requiring code modifications, dramatically reducing the time and cost to become quantum-safe across your estate.
4. Build long-term cryptographic agility:
Using NIST-standardised post-quantum algorithms (ML-KEM, ML-DSA), IBM and Northdoor help you build cryptographic agility into your architecture — so you can adapt as standards evolve and new threats emerge, without starting over each time.
IBM Quantum Safe toolkit
Three integrated modules for end-to-end quantum resilience
Quantum Safe Explorer:
Automated code scanning and CBOM generation. Discover every cryptographic asset across your codebase and infrastructure.
Guardium Quantum Safe:
Policy definition, compliance tracking, and vulnerability prioritisation via a unified security dashboard.
Quantum Safe Remediator:
Deploy post-quantum encryption without code changes using an adaptive proxy, the fastest route to protection.
Northdoor’s experts can assess your current cryptographic posture and map a clear path to quantum resilience — before the threat window closes.
Request a demo or contact sales on: 0207 448 8500
Explore security solutionsSubscribe to our newsletter to get the very latest insights and updates in the world of enterprise IT and data security: