What is the quantum encryption risk?
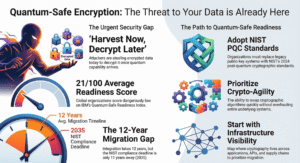
The quantum encryption risk refers to the vulnerability of current standards (like RSA and ECC) to future quantum computers. This includes “Harvest Now, Decrypt Later” attacks, where encrypted data is stolen today to be cracked once quantum technology matures.
Let us be direct: most organisations are not ready. The prevailing assumption in boardrooms across the UK is that quantum computing is a decade away and therefore somebody else’s problem. That assumption is wrong — and dangerously so. The threat is not theoretical. It is already operational, in the form of harvest now, decrypt later (HNDL) attacks, where state-level and sophisticated criminal actors are collecting encrypted data today with the explicit intention of decrypting it once quantum capability matures.
In 2024, the NIST finalised its first post-quantum cryptography standards, the clearest signal yet that governments consider Q-Day a credible near-term event. Estimates place it between 2030 and 2035. That is not far away when you consider that regulatory compliance, procurement cycles, and infrastructure migration can each take years in their own right.
The question for every organisation is not whether quantum computing will affect you. It will. The question is whether you will have conducted your quantum vulnerability assessment in time to do anything about it.

The quantum threat: key milestones
2016 NIST launches Post-Quantum Cryptography standardisation project, signalling that RSA and ECC have a finite lifespan
2024 NIST finalises first PQC standards: CRYSTALS-Kyber (ML-KEM) and CRYSTALS-Dilithium (ML-DSA) — the new baseline for quantum-safe encryption
2030–2035 Estimated arrival of Q-Day — the moment a cryptographically relevant quantum computer can break RSA-2048 in hours.
Where most organisations are getting this wrong
The most common mistake we see is conflating awareness with action. Organisations know quantum computing is coming. Very few have taken the concrete first steps to understand their actual exposure. Without a structured cryptographic vulnerability assessment, you cannot know your true quantum encryption risk or which data is most exposed. You are, in effect, flying blind.
The second mistake is treating this as purely an IT problem. It is not. The data most valuable to quantum-capable adversaries tends to be the data organisations are least willing to discuss openly: long-lived intellectual property, sensitive financial records, healthcare information, and strategic communications. The risk is existential for some organisations. It belongs in the boardroom, not just the server room.
Five steps to assess your quantum encryption vulnerability
A structured assessment does not need to be paralysing. The following five steps give organisations a practical, prioritised starting point — one that can be initiated immediately, regardless of where you currently sit on the digital maturity curve.
Your Quantum Risk Assessment: First Steps
Step 1. Conduct a Cryptographic Inventory:
Map every encryption algorithm in use across your applications, databases, APIs, and communications infrastructure. Flag RSA, ECC, and Diffie-Hellman protocols — these are the algorithms Shor’s algorithm dismantles most efficiently on a sufficiently powerful quantum machine.
Step 2. Classify Data by Sensitivity and Longevity:
Not all data carries equal risk. Identify what must remain confidential for ten years or more. Financial records, healthcare data, and intellectual property held today are already viable HNDL targets. This classification determines your migration priority order.
Step 3. Audit third-party and supply chain exposure:
Your quantum security posture is only as strong as your most vulnerable supplier. Audit every cloud provider, SaaS platform, and third-party integration for their post-quantum readiness. A single weak link in the chain can undermine every other step you take.
Step 4. Benchmark against NIST post-quantum standards:
Compare your current cryptographic stack against NIST’s 2024 finalised PQC standards — CRYSTALS-Kyber and CRYSTALS-Dilithium. Every gap you identify is a concrete migration task. This is the bridge between assessment and action.
Step 5. Build a crypto-agility roadmap:
Crypto-agility, the capacity to swap cryptographic algorithms without re-architecting your systems, is your long-term defence. Design for it now. Prioritise your highest-risk systems first, set measurable milestones, and treat migration as a continuous programme, not a one-time project.
The honest assessment
Organisations that begin this work now will find it manageable. Those that wait until Q-Day is imminent will face a very different reality: compressed timelines, regulatory pressure, and the near-certainty that some of their most sensitive data has already been harvested and is sitting in an adversary’s archive, waiting.
The cryptographic foundations that have underpinned digital security for three decades are approaching the end of their useful life. That is not a cause for panic. It is a call for structured, urgent action, beginning with an honest assessment of where you actually stand.
The quantum clock is ticking. The organisations that own their response to this will be the ones still standing when it strikes.