Cost-Effective Cybersecurity for SMEs: Protecting Your Business from Data Breaches and Cyber Attacks
As a small business, it can be difficult to keep up with the ever-evolving world of cybersecurity. In this video, Rob Batters, Director of Managed & Technical Services at Northdoor, outlines cost-effective cybersecurity for SMEs. Northdoor offers managed cybersecurity services to help protect your business from data breaches and cyber-attacks.
Video Transcription: Managed Cybersecurity Services
Cybersecurity eh!
Hackers.
Bad actors. State-sponsored cybercrime.
Not to mention regulatory considerations.
Thinking about it, now that I’ve mentioned it.
What about data breaches and accidental data loss?
And what about the other guy?
You know, the one in your supply chain?
Who does a great job for you.
What’s his security like?
Is it as good as yours?
What does it cost to put things right after a cyber attack?
Are we sleepwalking into a disaster?
If you’re not a big business with a team full of security professionals and a big I.T. budget, how on earth do you keep up?
What is the smaller business supposed to do?
Hello.
My name is Rob Batters and I’m the Director of Managed & Technical Services at Northdoor
And we have some answers for you.
Let’s talk about cost-effective cybersecurity for the SME.
So, what exactly is the cost of a data breach?
Well, there’s remedial work by specialists to be paid for.
Maybe a lot of vulnerabilities to address, not to mention some of the numbers attributed to ransom demands.
But, after all that, what about the cost to your business’s reputation?
I mean, after all, it takes a long time to build a reputation, but it can be completely ruined by a cyber attack in minutes.
Let’s have a look at some data.
IBM published an annual data breach report. It’s available online to anyone.
Here are some headline figures from the latest edition.
The average cost of a data breach in the UK is, roughly speaking, 5 million pounds.
The largest share of data breach costs was detection and escalation.
19% of breaches occurred because of a compromise at a business partner.
And phishing accounted for 16% of breaches.
76% of critical infrastructure organisations did not deploy a zero-trust architecture.
Sceptical?
So let’s look at an alternative source.
How about I back that up with something from the U.K. government?
Just like IBM.
The DCMS produces an annual report.
Here’s what they say.
39% of UK businesses identified a cyber attack.
The most common threat factor was phishing attempts, 83%.
31% of businesses and 26% of charities estimate they were attacked at least once.
Only 19% of businesses have a formal incident response plan, and only 13% of businesses assess the risks posed by their supply chain.
Two different opinions, two completely different sources, but more or less the same conclusions.
All of this brings me to our offering and how we can help.
What’s important to you?
What if you could build a mix and match your secure managed service to meet your requirements?
What if you could fix the basics?
Protect first what matters to your business and be ready to react properly to all these other threats.
Managed Cybersecurity Services for SMEs
Introducing our secure managed service.
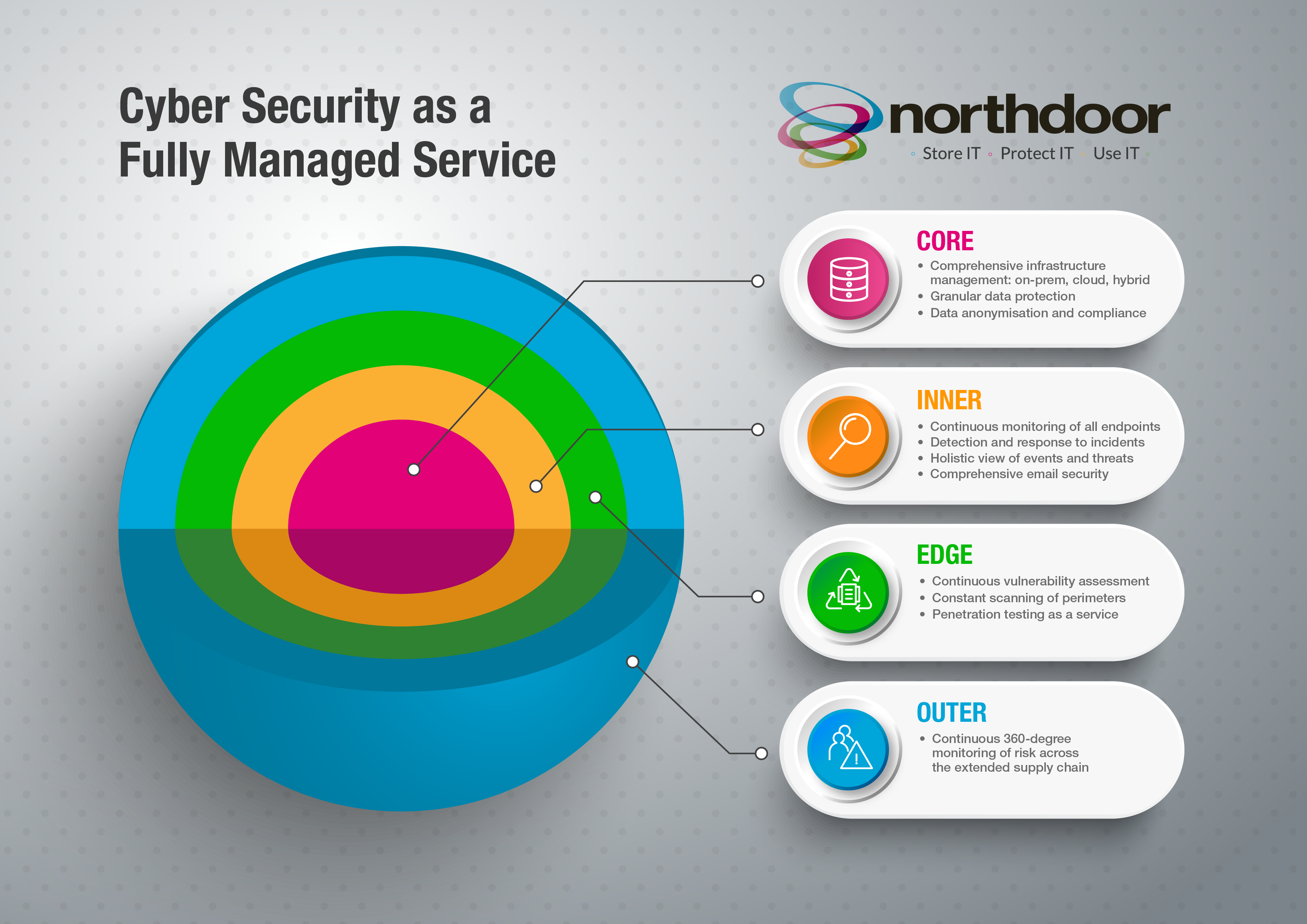
Now, we’ve designed our service in four independent yet integrated layers, and with our help, you can decide which is right for you.
We call these layers the core, the inner layer, the edge and the outer layer.
Let’s take a look at each one.
The core
The core. At the heart of your organisation is its data.
Our managed infrastructure services for on-premise, hybrid and cloud environments combined with data protection and sensitive data management services for databases.
Keep your systems running and give you control and compliance where it matters most, at the core.
The inner layer
The inner layer of our intelligent email solutions for phishing and data leakage detects and reduces human-activated risks.
People risks.
Inbound emails, outbound emails. We leave too much to our co-workers.
Let’s help them.
Both IBM and the DCMS reports were clear.
Phishing is big business, and we can help you mitigate against it; our managed detection and response service protects your endpoints, including those in the cloud and detects threats with rapid containment and remediation.
Remember, IBM’s report said that the largest share of data breach costs was down to this issue alone.
The edge
Now we supply smart vulnerability management with continuous perimeter scanning and regular vulnerability scanning with remediation.
Need PEN testing?
Of course, you do.
But that once-a-year test is really not enough.
We can add PEN testing as a service with retests on demand.
The outer layer
Finally, the outer layer.
Address your supply chain risk by scanning and rating their security.
Perform risk assessments and compare your suppliers.
Our Sanctions Checking solution enables you to check your clients against international financial sanctions lists on an ongoing basis.
The DCMS report clearly said that only 13% of businesses had assessed their supply chain risk, and IBM said that nearly a fifth of breaches occurred because of a compromise at a business partner.
We think it helps to think of I.T. security as a series of layers, each one addressing one or more risk defence in depth where you need it.
Cybersecurity is a big field, but with our help, you can identify what matters most, address the key issues and reduce your risk.
Thank you for your time. We’d love to help.
Cybersecurity as a fully managed service
If you are interested in securing your SME, contact Northdoor to learn about our managed security services.
Request a demo or contact sales on: 0207 448 8500
Contact us to learn about our managed security serviceLatest Blog Articles
Subscribe to our newsletter
Subscribe to our newsletter to get the very latest insights and updates in the world of enterprise IT and data security: